Attention as a Source of Scarcity for Decentralized Identity Systems
This document was originally published here. This paper proposes a new approach to introducing scarcity into identity systems without sacrificing privacy and self-sovereignty.
The method relies on quantifying attention flows between identities. It is predicated on attention being a basic element of all cognitive processes. It is also limited and therefore is a natural source of scarcity.
Problem
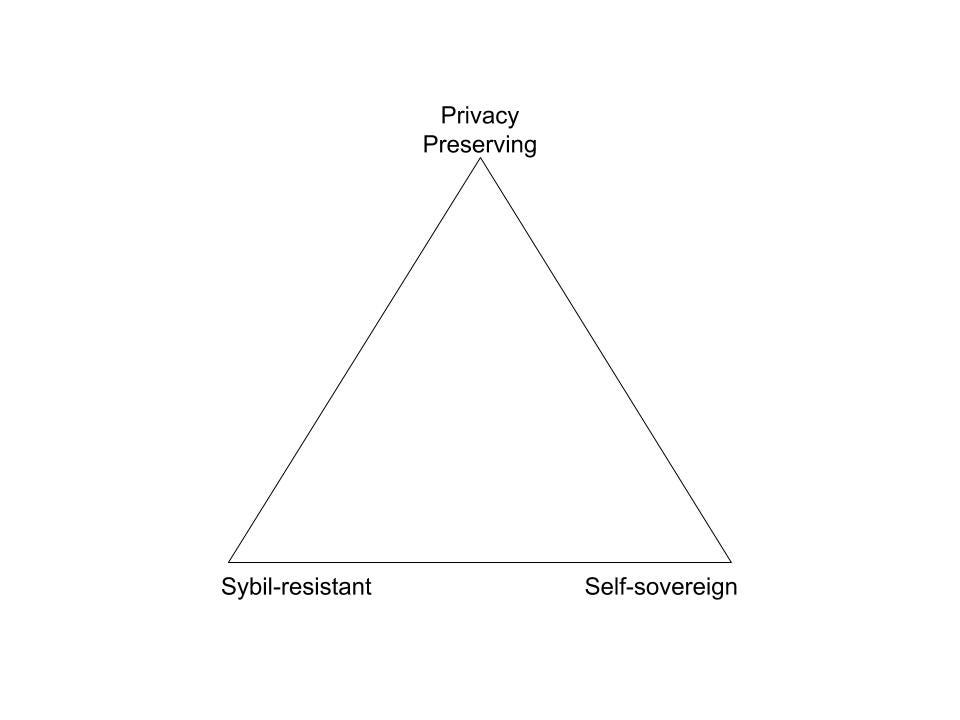
None of the designs for decentralized identity systems has been able to deliver on all three of the following features:
Privacy-preserving
Self-sovereignty
Sybil-resistant
I previously proposed to refer to this problem as Decentralized Identity Trilemma (Laskus 2018) ((Laskus, M. (2018, August 13). Decentralized Identity Trilemma. Retrieved February 22, 2019, from https://maciek.blog/dit)).
Requirements for a Solution
In order to address DIT, one needs to provide Sybil-resistance without sacrificing privacy and self-sovereignty:
No requirement to provide any ‘real name’1 documentation or credentials
No hindering users’ ability to create and control identifiers, including any limitation in how many, can be created.
Solution
Identity is a collection of ideas that others have about a subject2. The creation of an idea requires paying attention.
Attention is a basic component of all cognitive processes (Anderson, J.R. 2014) ((Anderson, J.R. (2014). Cognitive Psychology and Its Implications. Worth Publishers, 53–78.)). In that sense, it plays a similar role in the brain to electricity in a computer.
Both the computer and the brain can perform various types of computations. However, all of them require electricity and attention, respectively.
I can walk on a slackline, try to find a pattern in a string of numbers, or plan what to cook for dinner. My brain is flexible enough to perform each one of these tasks, even though they require different forms of intelligence3.
However, what they all have in common is that they require attention. I can switch between these different forms of intelligence, but I cannot use them all at the same time.
Attention is scarce. We can hold only a handful of objects in our attention at a given point in time (Byrne and Anderson 2001) ((Byrne, M. D., & Anderson, J. R. (2001). Serial modules in parallel: The psychological refractory period and perfect time-sharing. Psychological Review, 108, 847–869.)).
Making up an idea about somebody is another type of computation that our brain performs and is subject to the same limitation as other cognitive processes.
Not only making up an idea about somebody requires paying attention to that person. Additionally, we dedicate different amounts of attention to different people depending on how important we perceive them to be in a group.
This claim is axiomatic. You can observe it from your own experience.
A person with the highest status in a group will receive a lot of attention from the group members. A person with a low status is going to receive little attention.
This is true in a boardroom, in a bar, at a conference, or on Twitter.
This last claim has been verified empirically by my team. We have designed an algorithm that has mapped and ranked members of the “crypto Twitter.” It is based exclusively on tracking attention flows between members of this group.
The hypothesis that the results are accurate has been supported through an experiment of exposing the results to a large number of members of this group and observing their reactions (Laskus 2018) ((Laskus, M. (2018, March 8). What is Influence. Retrieved February 22, 2019, from https://maciek.blog/influence)).
It seems feasible that this approach can be applied to various other data sets.4
Conclusion
The proposed solution fulfills both requirements:
It does not require sacrificing privacy. One can create a pseudonymous account and attract the attention of other users. However, to do so, they must compete with others and provide something of interest. Not only does this process take a lot of time and effort, but it also seems to be an effective way of filtering between organic and machine intelligence products. We have seen hardly any bots receiving meaningful scores in our system.
It does not limit one’s ability to issue and control its identifiers. One can create as many as one wishes, but this process alone does not give them any “voting power.” In order for these identifiers to form identities, they need to become recognized by the intelligence behind other identities. Attracting their attention requires products of organic intelligence delivered over an extended time. Therefore, one can choose to create multiple identities. Still, their total weight/voting power will be predicated on the amount of attention the organic intelligence behind them can attract.